Overview
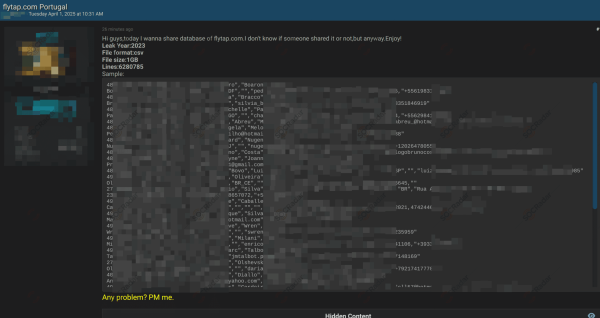
In early April 2025, a dark web post surfaced offering a 1GB dataset allegedly stolen from TAP Air Portugal, reportedly containing over 6.2 million records from 2023. Sample data indicates the presence of personally identifiable information (PII) such as names, emails, phone numbers, and potentially other sensitive customer or employee details.
The breach remains unverified, but the scale and structure of the data raise serious concerns, especially considering the aviation sector’s dependence on secure personal and operational data handling.
What Happened?
- Incident: Data leak offered on a well-known underground forum
- Claimed Dataset: 6.2M records from 2023 (1GB CSV file)
- Contents: Likely includes PII such as names, email addresses, and phone numbers
- Verification: Not confirmed by TAP or authorities
- Implications: Risk of phishing, fraud, regulatory exposure, and reputational damage
While authenticity is pending, the structure of the data and context suggest this could be an impactful leak or a prelude to further criminal activity targeting the aviation sector.
Relevance to Part-IS Compliance
Even if your organisation is not directly affected, this incident must be considered within your Part-IS compliance obligations:
- IS.I.OR.220 – Detection, Response, and Recovery
Requires capability to detect external threats and initiate internal containment if affected. - IS.I.OR.205 – Risk Assessment
Treat this as a valid scenario for threat modelling, especially if similar systems or vendors are used. - IS.I.OR.215 – Internal Reporting
Personnel must know how to report potential data misuse or targeted phishing. - IS.I.OR.230 – External Reporting
Should a similar breach be detected internally, the 72-hour rule for notification applies.
Recommended Actions
Strengthen Technical Controls:
- Enforce Multi-Factor Authentication (MFA) across all public-facing systems.
- Monitor for credential reuse or leaks tied to your domains.
- Audit user accounts for weak or reused passwords, especially for admin-level access.
- Segment access to limit exposure of customer and employee data.
Address Human and Operational Risk:
- Deploy anti-phishing protections and reinforce impersonation training.
- Inform customer-facing teams about possible scam emails referencing TAP or your brand.
- Run social engineering simulations targeting high-risk roles (ops, HR, support).
Regulatory & Reputational Readiness:
- Review data breach notification obligations under GDPR or local regulations.
- Pre-prepare a public response strategy and update your external contact templates.
- Brief legal and compliance teams to assess whether shared vendors or systems may be affected.
Why This Matters
Even without confirmation, this incident underscores critical lessons:
- PII breaches in aviation can lead to phishing of passengers, manipulation of crew workflows, or identity-based fraud targeting staff.
- Credential reuse attacks often follow large-scale leaks, potentially compromising operational platforms.
- Reputational harm can occur regardless of breach authenticity, affecting ticket sales, loyalty, and regulatory perception.
Aviation organisations should use this as an opportunity to test reporting pathways, validate ISMS response procedures, and remind staff of their role in preventing lateral threats that may stem from seemingly unrelated breaches.